Middle East Conflict Stirs Cybersecurity Space; Preparedness of India Inc. in Spotlight
Nasscom asks businesses to step up vigilance and preparedness across businesscontinuity and cybersecurity frameworks.

Opinions expressed by Entrepreneur contributors are their own.
You're reading Entrepreneur India, an international franchise of Entrepreneur Media.
The ongoing conflict in the Middle East has stirred the cybersecurity space with malicious actors changing their modus operandi to target individuals and businesses alike. The rise in malicious activities is testing readiness of the organizations worldwide.
Cybersecurity firm ThreatLabz reports that it has identified more than 8,000 newly registered domains with keywords linked to the Middle East conflict and events. The security firm says that most of these domains don’t have any content but warns that these could be leveraged to conduct malicious activities in the future. An analysis reveals that the active domains are trying to lure users by offering conflict monitoring, conflict-themed memecoins, merchandise, blogs, and even games. They also feature scam or betting-related Progressive Web Apps (PWAs).
Even as typical malicious actors are taking advantage of the conflict, there are also state-linked or aligned actors operating. According to Palo Alto Networks’ Unit 42 research team, Iran conducted several campaigns in response to the attacks and that there is a rise in cyberattacks conducted by individuals/groups operating outside the country, reports Intelligentcio.
While the research team is assured that the nation-state groups’ attacks may reduce with limited connectivity in Iran, but threat actors outside the regions could continue to conduct attacks though impact could be of low to medium significance.
“Cybercriminals are reportedly capitalizing on the conflict in the United Arab Emirates in a social engineering vishing scam to steal credentials. The threat actors call potential victims impersonating the Ministry of Interior, claiming to be confirming receipt of a national alert and prompting for the victim’s Emirates Identification Number (EID) for verification,” the research team said in a post.
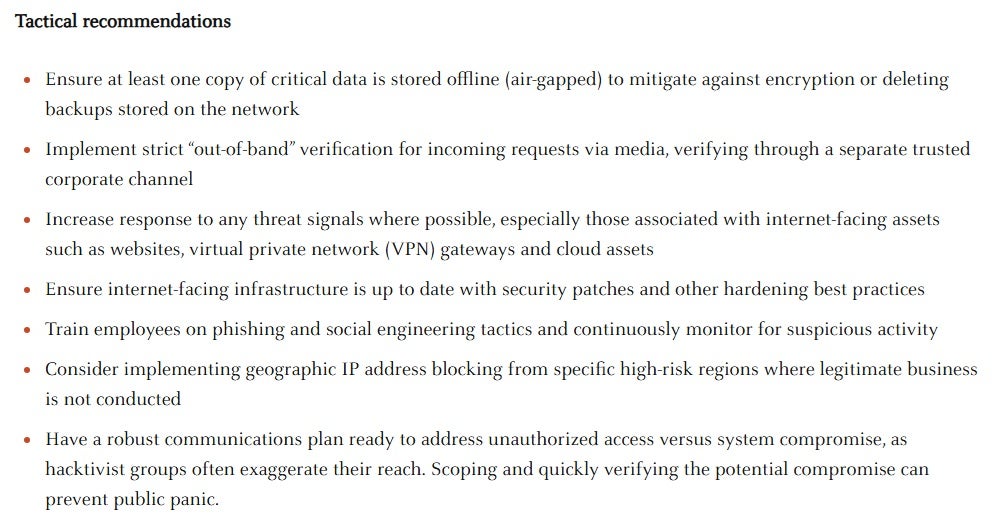
Pao Alto’s recommendations for organizations
“The ransomware-as-a-service (RaaS) group Tarnished Scorpius (aka INC Ransomware) has listed on its leak site an Israeli industrial machinery company, and replaced the company logo with a swastika.”
According to Khushhal Kaushik of Lisianthus Tech, cyber operations are increasingly becoming part of hybrid warfare, serving as tools for disruption, espionage, and retaliation without direct kinetic engagement. This “digital front” allows state and non-state actors to inflict significant economic damage, spread misinformation, and probe for vulnerabilities.
He also cited some recent examples: Iranian Retaliatory Cyber Campaigns Following the US/Israeli military strikes on Iranian nuclear and military sites on February 28, 2026, Iran-linked groups (e.g., those affiliated with the Islamic Revolutionary Guard Corps) launched large-scale phishing, DDoS attacks, and dangerous wiper malware against Israeli and US-linked entities. Unit 42 reported an increase in hacktivist activity, which included defacing Iranian government websites in early March, but also targeting intrusions into US financial apps.
“Increasing Attacks on Regional Infrastructure In the UAE, authorities intercepted 90,000–200,000 cyberattacks daily as of February 18, 2026, with over 70% of these involving DDoS attacks targeting the telecom and energy sectors. Similarly, AWS data centers in the UAE and Bahrain were shut down in early March due to sabotage-related disruptions, impacting cloud services worldwide.
Hacktivists and opportunists: Groups like Anonymous Sudan (Iran-backed) launched DDoS attacks on US media and Israeli ports, while pro-Palestinian hackers targeted Saudi Aramco with ransomware in late February. These combine government-sponsored and grassroots efforts, exploiting chaos for perceived or monetary gain.
Direct Cyber Incidents: While no major breaches have occurred yet, essential sectors like banking and energy have faced DDoS probes. IT giants like Wipro have seen increased vendor scrutiny costs.
Indirect Impact: Global cyber fatigue has diverted budgets—IDC estimates that Middle East/Africa IT spending will decline by 5-7% by 2026, which will have indirect impacts on Indian outsourcers (e.g., delays in contracts with UAE clients). According to an EY survey, geopolitical risk insurance premiums have increased by 15-20% for exposed firms. Furthermore, talent mobility issues have slowed the adoption of hybrid work setups, creating remote access gaps,” he added.
India’s Preparedness
While the impact of the conflict on the Indian digital ecosystem is currently minimal or non-existent, experts warn that a prolonged situation might eventually extend its effects here as well.
For instance, industry body Nasscom has issued a fresh advisory to member companies to step up vigilance and preparedness across business continuity and cybersecurity frameworks.
While business operations currently remain stable, organizations are proactively reviewing contingency plans and strengthening resilience measures to mitigate potential disruptions should the situation evolve over time, the industry body added in its advisory.
Speaking to Entrepreneur India, V4WEB Cybersecurity founder Ritesh Bhatia explained that the situation in the Middle East shows how cyber activity often happens alongside military operations.
“We have seen several hacktivist groups launching DDoS attacks on government websites, media platforms, and financial institutions connected to the countries involved in the conflict. Security researchers have also reported attempts by state-linked groups to target energy systems and other critical infrastructure. In some cases attackers have tried to access internet-connected cameras and devices to gather intelligence. This shows that cyber operations are now part of modern warfare and not just an IT issue,” he said.
Mohammed Rizvan, Threat Intelligence Researcher at CloudSEK tells Entrepreneur that cyber operations have become a central part of modern geopolitical conflicts. In the ongoing Middle East crisis, cyber capabilities are being used alongside conventional military operations for intelligence gathering, disruption of infrastructure, and psychological warfare.
“One example is the surge in cyber activity by pro-Iran and pro-Israel hacktivist groups targeting government websites, financial services, and critical infrastructure. Groups such as CyberAv3ngers, Handala, and others have launched distributed denial-of-service (DDoS) attacks and website defacements against entities perceived to support opposing sides,” the firm adds.
Bhatia also appealed to India Inc. that they should treat geopolitical conflicts as a potential cybersecurity risk even if the conflict is happening far away.
He recommends that organisations should increase monitoring of cyber threats and keep track of global threat intelligence related to the region. Strong identity controls such as multi-factor authentication are important because many attacks begin with stolen credentials or phishing emails.
Companies should also review their supply chain security since attackers often target vendors or smaller partners to enter larger organisations. At the same time businesses should ensure that their incident response and business continuity plans are ready in case of any cyber disruption, he said.
Nasscom’s advisory is also not very different from Bhatia’s as the industry body says its member companies are evaluating alternate infrastructure routing to ensure cloud and data centre resilience and safeguard critical systems and organizations are proactively engaging with clients to communicate preparedness measures and ensure continuity of services, among other initiatives.
It further recommends:
Rotation of credentials organisation-wide and apply patches for critical CVEs.
Enforce multi-factor authentication on all external access paths (VPN, RDP, SSH, cloud admin) and implement conditional access controls to counter token-theft and adversary-in-the-middle attacks.
Assess all third-party vendors with Middle Eastern exposure. One compromised vendor can cascade into sector-wide disruption.
Engage ISPs and cloud providers for DDoS scrubbing capacity.
Maintain air-gapped backups for ICS/OT, core banking, and healthcare systems.
Experts believe that Nasscom’s advisory rightly focuses on strengthening operational and cyber resilience and asking companies to review travel risks and business continuity planning.
“However companies should also pay more attention to protecting connected infrastructure such as industrial systems, sensors, and IoT devices which are often targeted during cyber conflicts. Another important area is better threat intelligence sharing between industry, security firms, and government agencies so that emerging threats can be identified early. Organisations should also be aware of the rising risk of misinformation and deepfakes during geopolitical crises,” Bhatia cautioned.
Experts believe that one possible ripple effect is the expansion of cyber proxy wars, where state-aligned hacktivist groups target companies in allied or partner economies. Several companies with international operations may increasingly find themselves in the crosshairs of such campaigns.
“Another potential impact is disruption to physical infrastructure (as Iran has already targeted AWS Data centre, kinetically), including cloud services and telecom networks located in the region. Any instability affecting these systems could have downstream effects on businesses globally. According to Rizvan, prolonged geopolitical tensions often lead to an increase in disinformation campaigns and online fraud, which can affect corporate reputation and overall trust,” Rizwan added.
The ongoing conflict in the Middle East has stirred the cybersecurity space with malicious actors changing their modus operandi to target individuals and businesses alike. The rise in malicious activities is testing readiness of the organizations worldwide.
Cybersecurity firm ThreatLabz reports that it has identified more than 8,000 newly registered domains with keywords linked to the Middle East conflict and events. The security firm says that most of these domains don’t have any content but warns that these could be leveraged to conduct malicious activities in the future. An analysis reveals that the active domains are trying to lure users by offering conflict monitoring, conflict-themed memecoins, merchandise, blogs, and even games. They also feature scam or betting-related Progressive Web Apps (PWAs).
Even as typical malicious actors are taking advantage of the conflict, there are also state-linked or aligned actors operating. According to Palo Alto Networks’ Unit 42 research team, Iran conducted several campaigns in response to the attacks and that there is a rise in cyberattacks conducted by individuals/groups operating outside the country, reports Intelligentcio.






